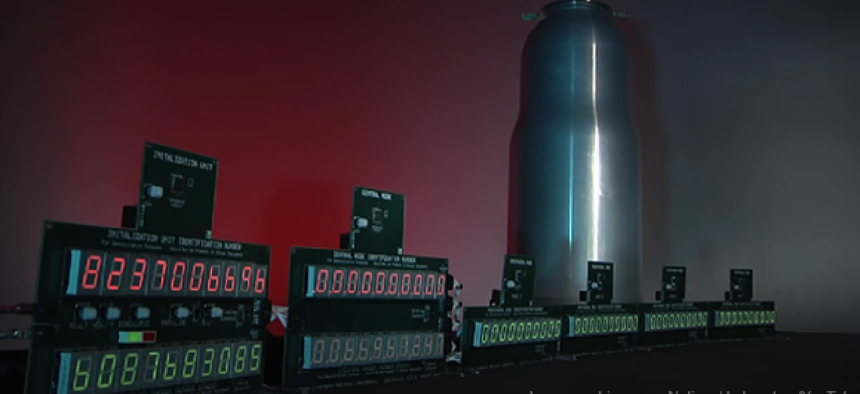
‘Gold standard’ for random number generation: radioactive decay

Connecting state and local government leaders
The technology used to control access to nuclear weapons could secure other applications that use encoded protection, such as communications and the IT supply chain.
The technology used to control access to nuclear weapons could secure other applications that use encoded protection, such as communications and the IT supply chain.
Intrinsic use control (IUC) uses a nuclear weapon’s fluctuating radiation fields to create complex, unique use control numbers, which protect the weapon and its components from unauthorized use.
The coding can lock down system components with an almost unknowable key if they're tampered with, essentially allowing the weapon to protect itself from outside meddling.
Because the code is randomly generated by its unique nuclear source, it's not known by any person, and therefore the possibility that it could be replicated is substantially reduced, said Mark Hart, a scientist and engineer at Lawrence Livermore National Laboratory.
"Using the random process of nuclear radioactive decay is the gold standard of random number generators," Hart said. "You'd have a better chance of winning both Mega Millions and Powerball on the same day than getting control of IUC-protected components."
The coding is imprinted on a nuclear weapon's components during assembly, with the unique IDs known only to the weapon. Any anomaly in the verification process, spurred by attempted removal or replacement of a protected component, shuts down all the components on the weapon, rendering it unusable, Hart said.
Although it might sound as though the technique has a very specific use, other agencies and industry could harness it to protect other IT hardware and communications, Hart said in an interview with FCW, GCN’s sister site.
Using a unique radiologically generated encryption key in the manufacturing process of IT equipment could prevent tampering and better secure the supply chain, Hart said.
The coding could even eliminate insider threats by preventing people from adding counterfeit components or tampering with the equipment, he added.
NEXT STORY: What’s next in cybersecurity automation




