Free cybersecurity tools for state, local governments
Free cybersecurity tools are available state, local, tribal and territorial government members of the Multi-State Information Sharing and Analysis Center and the Elections Infrastructure Information Sharing and Analysis Center – they just need to know to ask for them, experts said.
Getting facial recognition right
To realize the benefits of facial recognition while maintaining ethical integrity, agencies must ensure systems' accuracy, security and resistance to bias.
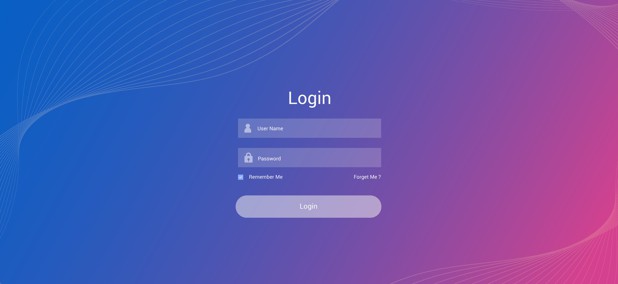
Agencies still rely on username-password for access management
Even though more secure identity access management solutions exist, 86% of federal, state and local government respondents said that usernames and passwords are their most-used authentication method, according to a recent survey.
How the Biden administration is making gains in an uphill battle against Russian hackers
Though government-controlled hackers might persist, and criminal groups might disappear, rebuild and rebrand, the high costs imposed by the Biden administration could hinder their success.
Small cities worry cybersecurity money won't reach them
Even though small, under-resourced municipalities often fall victim to cyberattacks, many don't have the resources to put together a proposal for a share of the $1 billion in federal cybersecurity grants available through the new infrastructure law.
Think twice before scanning that QR code, FBI warns
The FBI is warning that cybercriminals are tampering with QR codes to redirect victims to malicious sites that steal login and financial information.
ID verification, analytics can help agencies fight fraud
Combining an automated verification system and data analytics for prevention and detection helps create a powerful tool for government IT professionals facing a flood of fraud.
Maryland Health Department hit with ransomware
For more than two weeks, COVID surveillance data wasn't released publicly, and many day-to-day operational services are still unavailable.
The metaverse offers a future full of potential – for terrorists and extremists, too
The rise of the metaverse will open new vulnerabilities and give people with malicious intent novel opportunities to exploit them.
Cities in Texas hit by QR-code phishing scam
Austin, Houston and San Antonio have been affected by a phishing scam designed to get users to pay for parking using fraudulent QR codes pasted on public meters.
Maintaining zero trust over time: Why set-it and forget-it won’t work
Zero trust requires continuous revalidation of trustworthiness -- of the devices, services and identities connecting into an enterprise environment, as well as the systems to which they are connecting.
Avoid being held captive by ransomware with secure, reliable backups
After a ransomware attack, tiered recovery time objectives and a thorough, practiced plan can help agencies minimize downtime.
Cyber vulnerabilities could impact municipal finance
Municipal bond credit analysts consider governments unprepared for cyberattacks, a recent survey says.
Ohio adopts single sign-on for unemployment claims
The OH|ID gives users a trusted identity they can use for unemployment benefits, while offering state agencies enterprise-level identity proofing services.
5 best practices for strengthening your software supply chain with DevSecOps
Because every application is mission critical, strengthening DevSecOps processes provides needed transparency into an agency’s full portfolio of applications.
What is Log4j? A cybersecurity expert explains the latest internet vulnerability, how bad it is and what’s at stake
Simple to exploit, Log4j is used in cloud services as well as a wide range of programs from software development tools to security tools, which makes it easy for an army of bad actors to attack millions of systems.
When multifactor authentication for data security isn’t enough
Pre-boot authentication denies an attacker access to even a single data point – a viable option for federal agencies and critical infrastructure organizations securing data at rest.
7 cyber defense use cases
Whether facing data loss, ransomware, fraud or privacy threats, agencies can leverage technology and process solutions to help them prevent and respond to attacks.
Kronos ransomware attack impacting government employee paychecks
The cyberattack on the Kronos Private Cloud may last for weeks, affecting payroll and workforce management for many state and local government agencies.
The best way to protect personal biomedical data from hackers could be to treat the problem like a game
By accounting for the value of the shared data, the game-based approach finds strategies that strike the right balance between utility and privacy.

Do Not Sell My Personal Information
When you visit our website, we store cookies on your browser to collect information. The information collected might relate to you, your preferences or your device, and is mostly used to make the site work as you expect it to and to provide a more personalized web experience. However, you can choose not to allow certain types of cookies, which may impact your experience of the site and the services we are able to offer. Click on the different category headings to find out more and change our default settings according to your preference. You cannot opt-out of our First Party Strictly Necessary Cookies as they are deployed in order to ensure the proper functioning of our website (such as prompting the cookie banner and remembering your settings, to log into your account, to redirect you when you log out, etc.). For more information about the First and Third Party Cookies used please follow this link.
Manage Consent Preferences
Strictly Necessary Cookies - Always Active
We do not allow you to opt-out of our certain cookies, as they are necessary to ensure the proper functioning of our website (such as prompting our cookie banner and remembering your privacy choices) and/or to monitor site performance. These cookies are not used in a way that constitutes a “sale” of your data under the CCPA. You can set your browser to block or alert you about these cookies, but some parts of the site will not work as intended if you do so. You can usually find these settings in the Options or Preferences menu of your browser. Visit www.allaboutcookies.org to learn more.
Sale of Personal Data, Targeting & Social Media Cookies
Under the California Consumer Privacy Act, you have the right to opt-out of the sale of your personal information to third parties. These cookies collect information for analytics and to personalize your experience with targeted ads. You may exercise your right to opt out of the sale of personal information by using this toggle switch. If you opt out we will not be able to offer you personalised ads and will not hand over your personal information to any third parties. Additionally, you may contact our legal department for further clarification about your rights as a California consumer by using this Exercise My Rights link
If you have enabled privacy controls on your browser (such as a plugin), we have to take that as a valid request to opt-out. Therefore we would not be able to track your activity through the web. This may affect our ability to personalize ads according to your preferences.
Targeting cookies may be set through our site by our advertising partners. They may be used by those companies to build a profile of your interests and show you relevant adverts on other sites. They do not store directly personal information, but are based on uniquely identifying your browser and internet device. If you do not allow these cookies, you will experience less targeted advertising.
Social media cookies are set by a range of social media services that we have added to the site to enable you to share our content with your friends and networks. They are capable of tracking your browser across other sites and building up a profile of your interests. This may impact the content and messages you see on other websites you visit. If you do not allow these cookies you may not be able to use or see these sharing tools.
If you want to opt out of all of our lead reports and lists, please submit a privacy request at our Do Not Sell page.
Cookie List
A cookie is a small piece of data (text file) that a website – when visited by a user – asks your browser to store on your device in order to remember information about you, such as your language preference or login information. Those cookies are set by us and called first-party cookies. We also use third-party cookies – which are cookies from a domain different than the domain of the website you are visiting – for our advertising and marketing efforts. More specifically, we use cookies and other tracking technologies for the following purposes:
Strictly Necessary Cookies
We do not allow you to opt-out of our certain cookies, as they are necessary to ensure the proper functioning of our website (such as prompting our cookie banner and remembering your privacy choices) and/or to monitor site performance. These cookies are not used in a way that constitutes a “sale” of your data under the CCPA. You can set your browser to block or alert you about these cookies, but some parts of the site will not work as intended if you do so. You can usually find these settings in the Options or Preferences menu of your browser. Visit www.allaboutcookies.org to learn more.
Functional Cookies
We do not allow you to opt-out of our certain cookies, as they are necessary to ensure the proper functioning of our website (such as prompting our cookie banner and remembering your privacy choices) and/or to monitor site performance. These cookies are not used in a way that constitutes a “sale” of your data under the CCPA. You can set your browser to block or alert you about these cookies, but some parts of the site will not work as intended if you do so. You can usually find these settings in the Options or Preferences menu of your browser. Visit www.allaboutcookies.org to learn more.
Performance Cookies
We do not allow you to opt-out of our certain cookies, as they are necessary to ensure the proper functioning of our website (such as prompting our cookie banner and remembering your privacy choices) and/or to monitor site performance. These cookies are not used in a way that constitutes a “sale” of your data under the CCPA. You can set your browser to block or alert you about these cookies, but some parts of the site will not work as intended if you do so. You can usually find these settings in the Options or Preferences menu of your browser. Visit www.allaboutcookies.org to learn more.
Sale of Personal Data
We also use cookies to personalize your experience on our websites, including by determining the most relevant content and advertisements to show you, and to monitor site traffic and performance, so that we may improve our websites and your experience. You may opt out of our use of such cookies (and the associated “sale” of your Personal Information) by using this toggle switch. You will still see some advertising, regardless of your selection. Because we do not track you across different devices, browsers and GEMG properties, your selection will take effect only on this browser, this device and this website.
Social Media Cookies
We also use cookies to personalize your experience on our websites, including by determining the most relevant content and advertisements to show you, and to monitor site traffic and performance, so that we may improve our websites and your experience. You may opt out of our use of such cookies (and the associated “sale” of your Personal Information) by using this toggle switch. You will still see some advertising, regardless of your selection. Because we do not track you across different devices, browsers and GEMG properties, your selection will take effect only on this browser, this device and this website.
Targeting Cookies
We also use cookies to personalize your experience on our websites, including by determining the most relevant content and advertisements to show you, and to monitor site traffic and performance, so that we may improve our websites and your experience. You may opt out of our use of such cookies (and the associated “sale” of your Personal Information) by using this toggle switch. You will still see some advertising, regardless of your selection. Because we do not track you across different devices, browsers and GEMG properties, your selection will take effect only on this browser, this device and this website.