Your car could be at risk for cyber attacks
New research applies a popular criminal justice framework to smart car cybersecurity and provides recommendations for consistently, actively updating system software.
How state and local government can defend against identity attacks
By evaluating authorization at the individual level, agencies can mitigate some of the most credible threats and shift their focus back to improving citizen experience through innovation and modernization.
In search of better biometrics
The National Institute of Standards and Technology has released new biometric samples researchers can use to test their authentication technology.
Ransomware defense for local governments
The combination of a solid backup and disaster recovery plan with an effective vulnerability scanning and data breach emulation strategy will go a long way toward both preventing attacks and recovering from successful attacks.
Congress reaches deal for state election security grants
A spending deal in Congress gives the Election Assistance Commission $425 million in grant funding for states to upgrade their election infrastructure.
Solving identity management a 'game changer' for agencies
The General Services Administration wants an identity management framework that can be used across the federal government.
Kansas abandons technology trumpeted by Kris Kobach, Trump’s onetime voter fraud czar
A system supposedly meant to root out voter fraud was beset by security and accuracy issues.
3 steps to improve identity and access management without undermining productivity
A solid IAM program ensures the right users have the right access to the right applications without compromising security.
Top 25 software vulnerabilities
The Common Weakness Enumeration list's first update since 2011 ranks weaknesses based errors’ prevalence and severity.
Current encryption algorithms still strong, NIST official says
Agencies can slowly switch out their older encryption protocols over the coming years without leaving themselves exposed.
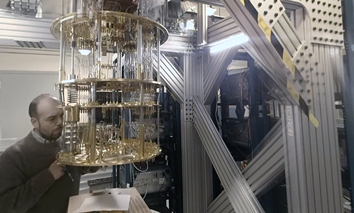
A quantum computing future is unlikely, due to random hardware errors
Error-correction, which is fundamental to a multi-purpose computer, poses such a significant challenge to quantum computers that it may prohibit their use at a commercial scale.
Credentialing private-sector emergency workers
The Corporate Emergency Access System makes it easier to verify that someone claiming to be essential company personnel is in fact essential.
Commerce tightening IT, telecom supply chain security
The Department of Commerce has proposed a new rule to identify, evaluate and address business transactions involving the use of Chinese-made telecommunications gear in U.S. infrastructure
4 tough questions (and answers) about orchestration
Security orchestration is about integrating and automating the entire cybersecurity ecosystem of information-gathering and enforcement products so IT teams can protect networks, systems and devices.
How TIC 3.0 enables modernization
The latest generation of the Trusted Internet Connection will make it easier for agencies to modernize as they move to the Enterprise Infrastructure Solutions telecommunications contract.
CISA partners on risk-limiting audit software for election systems
The Cybersecurity and Infrastructure Security Agency announced it is partnering with VotingWorks to further develop and pilot the organization's open-source election risk-limiting audit tool called Arlo.
'Quantum supremacy' demands prioritization of crypto protections
A combination of quantum key distribution and quantum resistant algorithms offers a defense-in-depth approach to the problems we face from quantum computers.
Automation strengthens facility threat assessments
The Federal Protective Service automated much of the information collection and analysis to identify security-related deficiencies at federal facilities and recommend countermeasure and mitigation measures.
10 ways states can avoid becoming ransomware victims
Identifying the vulnerabilities that pose the most imminent threat and have the capability to cause widespread damage can make patching both practical and sustainable.
Hackers are now targeting councils and governments, threatening to leak citizen data
Rather than denying victims access to their hostage data, leakware attackers threaten to publish citizens’ sensitive information online.

Do Not Sell My Personal Information
When you visit our website, we store cookies on your browser to collect information. The information collected might relate to you, your preferences or your device, and is mostly used to make the site work as you expect it to and to provide a more personalized web experience. However, you can choose not to allow certain types of cookies, which may impact your experience of the site and the services we are able to offer. Click on the different category headings to find out more and change our default settings according to your preference. You cannot opt-out of our First Party Strictly Necessary Cookies as they are deployed in order to ensure the proper functioning of our website (such as prompting the cookie banner and remembering your settings, to log into your account, to redirect you when you log out, etc.). For more information about the First and Third Party Cookies used please follow this link.
Manage Consent Preferences
Strictly Necessary Cookies - Always Active
We do not allow you to opt-out of our certain cookies, as they are necessary to ensure the proper functioning of our website (such as prompting our cookie banner and remembering your privacy choices) and/or to monitor site performance. These cookies are not used in a way that constitutes a “sale” of your data under the CCPA. You can set your browser to block or alert you about these cookies, but some parts of the site will not work as intended if you do so. You can usually find these settings in the Options or Preferences menu of your browser. Visit www.allaboutcookies.org to learn more.
Sale of Personal Data, Targeting & Social Media Cookies
Under the California Consumer Privacy Act, you have the right to opt-out of the sale of your personal information to third parties. These cookies collect information for analytics and to personalize your experience with targeted ads. You may exercise your right to opt out of the sale of personal information by using this toggle switch. If you opt out we will not be able to offer you personalised ads and will not hand over your personal information to any third parties. Additionally, you may contact our legal department for further clarification about your rights as a California consumer by using this Exercise My Rights link
If you have enabled privacy controls on your browser (such as a plugin), we have to take that as a valid request to opt-out. Therefore we would not be able to track your activity through the web. This may affect our ability to personalize ads according to your preferences.
Targeting cookies may be set through our site by our advertising partners. They may be used by those companies to build a profile of your interests and show you relevant adverts on other sites. They do not store directly personal information, but are based on uniquely identifying your browser and internet device. If you do not allow these cookies, you will experience less targeted advertising.
Social media cookies are set by a range of social media services that we have added to the site to enable you to share our content with your friends and networks. They are capable of tracking your browser across other sites and building up a profile of your interests. This may impact the content and messages you see on other websites you visit. If you do not allow these cookies you may not be able to use or see these sharing tools.
If you want to opt out of all of our lead reports and lists, please submit a privacy request at our Do Not Sell page.
Cookie List
A cookie is a small piece of data (text file) that a website – when visited by a user – asks your browser to store on your device in order to remember information about you, such as your language preference or login information. Those cookies are set by us and called first-party cookies. We also use third-party cookies – which are cookies from a domain different than the domain of the website you are visiting – for our advertising and marketing efforts. More specifically, we use cookies and other tracking technologies for the following purposes:
Strictly Necessary Cookies
We do not allow you to opt-out of our certain cookies, as they are necessary to ensure the proper functioning of our website (such as prompting our cookie banner and remembering your privacy choices) and/or to monitor site performance. These cookies are not used in a way that constitutes a “sale” of your data under the CCPA. You can set your browser to block or alert you about these cookies, but some parts of the site will not work as intended if you do so. You can usually find these settings in the Options or Preferences menu of your browser. Visit www.allaboutcookies.org to learn more.
Functional Cookies
We do not allow you to opt-out of our certain cookies, as they are necessary to ensure the proper functioning of our website (such as prompting our cookie banner and remembering your privacy choices) and/or to monitor site performance. These cookies are not used in a way that constitutes a “sale” of your data under the CCPA. You can set your browser to block or alert you about these cookies, but some parts of the site will not work as intended if you do so. You can usually find these settings in the Options or Preferences menu of your browser. Visit www.allaboutcookies.org to learn more.
Performance Cookies
We do not allow you to opt-out of our certain cookies, as they are necessary to ensure the proper functioning of our website (such as prompting our cookie banner and remembering your privacy choices) and/or to monitor site performance. These cookies are not used in a way that constitutes a “sale” of your data under the CCPA. You can set your browser to block or alert you about these cookies, but some parts of the site will not work as intended if you do so. You can usually find these settings in the Options or Preferences menu of your browser. Visit www.allaboutcookies.org to learn more.
Sale of Personal Data
We also use cookies to personalize your experience on our websites, including by determining the most relevant content and advertisements to show you, and to monitor site traffic and performance, so that we may improve our websites and your experience. You may opt out of our use of such cookies (and the associated “sale” of your Personal Information) by using this toggle switch. You will still see some advertising, regardless of your selection. Because we do not track you across different devices, browsers and GEMG properties, your selection will take effect only on this browser, this device and this website.
Social Media Cookies
We also use cookies to personalize your experience on our websites, including by determining the most relevant content and advertisements to show you, and to monitor site traffic and performance, so that we may improve our websites and your experience. You may opt out of our use of such cookies (and the associated “sale” of your Personal Information) by using this toggle switch. You will still see some advertising, regardless of your selection. Because we do not track you across different devices, browsers and GEMG properties, your selection will take effect only on this browser, this device and this website.
Targeting Cookies
We also use cookies to personalize your experience on our websites, including by determining the most relevant content and advertisements to show you, and to monitor site traffic and performance, so that we may improve our websites and your experience. You may opt out of our use of such cookies (and the associated “sale” of your Personal Information) by using this toggle switch. You will still see some advertising, regardless of your selection. Because we do not track you across different devices, browsers and GEMG properties, your selection will take effect only on this browser, this device and this website.
Help us tailor content specifically for you: