Phishing protection boosts mobile security
The Lookout mobile security platform spots phishing attempts in emails, texts, social media posts, apps or websites.
Protecting the 'right to be forgotten' in the age of blockchain
A new blockchain model allows users to temporarily store, summarize or completely remove their transactions from blockchain, while maintaining the ledger's consistency.
Are elections any more secure than in 2016?
Although $400 million has been set aside to address vulnerabilities, it's just a drop in the bucket compared to what states and election security experts say is needed to fix the problem.
5 ways to keep email hacking from damaging your public life
With the midterm elections just around the corner, candidates and government officials must take extra care to ensure their communications are secure.
Illuminating the ‘dark web’
People often think of the dark web as a place where criminals sell drugs or exchange stolen information -- or as a rare section of the internet Google can’t crawl. It’s both, and neither, and much more.
What you need to know about election security
Separate the signal from the noise with this multipart overview of election-security concerns.
Could civilians help fill the cyber talent gap?
With the growing need for cybersecurity experts, the government is missing a chance to take advantage of volunteers and part-time talent, a new report says.
DOD turns up the heat with bug bounties
The Pentagon is bringing on new security firms to participate in the programs and broadening the focus to include "high-value" Defense Department assets.
As digital threats grow, will cyber insurance take off?
Although cyberattacks have become increasingly sophisticated, the cyber insurance market’s extremely small size suggests that organizations might have underrated its importance.
My thoughts are my password, because my brain reactions are unique
A "brain password" is a mix of the person’s unique biological brain structure and their involuntary memory that determines how it responds to a particular stimulus.
State CISOs gain stature, but still struggle with funding and workforce
A new survey from Deloitte and NASCIO shows how state governments are managing cybersecurity demands.
In fighting fraud, the only constant is change
Agencies must invest the time and resources in risk assessments, vulnerability studies, internal skill improvement and data analytics to make increasingly informed decisions about their susceptibility to fraud.
When cybersecurity capabilities are paid for, but untapped
Agencies should cull the security stack and provide contextual visibility across all layers of the environment -- network, endpoint, lateral movement, cloud and IoT.
Securing critical infrastructure against modern vulnerabilities and cyberthreats
By proactively conducting threat research, segmenting networks and deploying proper security hygiene, critical infrastructure providers will be better prepared to identify threats, secure networks against them and mitigate any resulting damage.
LA's cyber strategy: savvier employees, secure IoT
Los Angeles is reducing its attack surface by training employees and securing connected devices.
6 growing threats to network security
The network has become not only a target but also a channel for disruption -- distributing DDoS, phishing, ransomware and other types of malware attacks.
Blockchains won’t fix internet voting security -- and could make it worse
Officials and companies who promote online voting are creating a false sense of security –- and putting the integrity of the election process at risk.
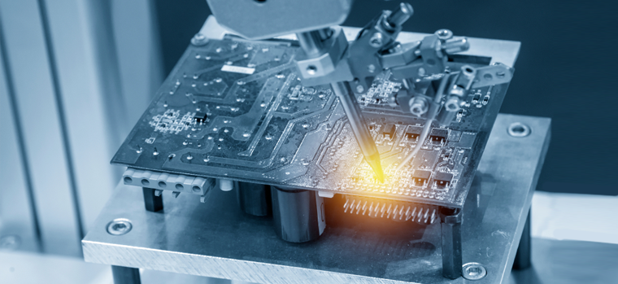
Open-source hardware could defend against the next generation of hacking
When devices' designs and components are open for public view, downstream customers could verify the security themselves.
Tackling privileged-access security
To prevent attackers from infiltrating government networks, agencies must secure privileged access, limiting intruders’ ability to move laterally and escalate privileges.
Biometric ID spots imposters at land crossing
Customs and Border Protection’s biometric entry/exit identification system nabbed two men attempting to cross from Mexico into the U.S. using someone else’s border-crossing cards.

Do Not Sell My Personal Information
When you visit our website, we store cookies on your browser to collect information. The information collected might relate to you, your preferences or your device, and is mostly used to make the site work as you expect it to and to provide a more personalized web experience. However, you can choose not to allow certain types of cookies, which may impact your experience of the site and the services we are able to offer. Click on the different category headings to find out more and change our default settings according to your preference. You cannot opt-out of our First Party Strictly Necessary Cookies as they are deployed in order to ensure the proper functioning of our website (such as prompting the cookie banner and remembering your settings, to log into your account, to redirect you when you log out, etc.). For more information about the First and Third Party Cookies used please follow this link.
Manage Consent Preferences
Strictly Necessary Cookies - Always Active
We do not allow you to opt-out of our certain cookies, as they are necessary to ensure the proper functioning of our website (such as prompting our cookie banner and remembering your privacy choices) and/or to monitor site performance. These cookies are not used in a way that constitutes a “sale” of your data under the CCPA. You can set your browser to block or alert you about these cookies, but some parts of the site will not work as intended if you do so. You can usually find these settings in the Options or Preferences menu of your browser. Visit www.allaboutcookies.org to learn more.
Sale of Personal Data, Targeting & Social Media Cookies
Under the California Consumer Privacy Act, you have the right to opt-out of the sale of your personal information to third parties. These cookies collect information for analytics and to personalize your experience with targeted ads. You may exercise your right to opt out of the sale of personal information by using this toggle switch. If you opt out we will not be able to offer you personalised ads and will not hand over your personal information to any third parties. Additionally, you may contact our legal department for further clarification about your rights as a California consumer by using this Exercise My Rights link
If you have enabled privacy controls on your browser (such as a plugin), we have to take that as a valid request to opt-out. Therefore we would not be able to track your activity through the web. This may affect our ability to personalize ads according to your preferences.
Targeting cookies may be set through our site by our advertising partners. They may be used by those companies to build a profile of your interests and show you relevant adverts on other sites. They do not store directly personal information, but are based on uniquely identifying your browser and internet device. If you do not allow these cookies, you will experience less targeted advertising.
Social media cookies are set by a range of social media services that we have added to the site to enable you to share our content with your friends and networks. They are capable of tracking your browser across other sites and building up a profile of your interests. This may impact the content and messages you see on other websites you visit. If you do not allow these cookies you may not be able to use or see these sharing tools.
If you want to opt out of all of our lead reports and lists, please submit a privacy request at our Do Not Sell page.
Cookie List
A cookie is a small piece of data (text file) that a website – when visited by a user – asks your browser to store on your device in order to remember information about you, such as your language preference or login information. Those cookies are set by us and called first-party cookies. We also use third-party cookies – which are cookies from a domain different than the domain of the website you are visiting – for our advertising and marketing efforts. More specifically, we use cookies and other tracking technologies for the following purposes:
Strictly Necessary Cookies
We do not allow you to opt-out of our certain cookies, as they are necessary to ensure the proper functioning of our website (such as prompting our cookie banner and remembering your privacy choices) and/or to monitor site performance. These cookies are not used in a way that constitutes a “sale” of your data under the CCPA. You can set your browser to block or alert you about these cookies, but some parts of the site will not work as intended if you do so. You can usually find these settings in the Options or Preferences menu of your browser. Visit www.allaboutcookies.org to learn more.
Functional Cookies
We do not allow you to opt-out of our certain cookies, as they are necessary to ensure the proper functioning of our website (such as prompting our cookie banner and remembering your privacy choices) and/or to monitor site performance. These cookies are not used in a way that constitutes a “sale” of your data under the CCPA. You can set your browser to block or alert you about these cookies, but some parts of the site will not work as intended if you do so. You can usually find these settings in the Options or Preferences menu of your browser. Visit www.allaboutcookies.org to learn more.
Performance Cookies
We do not allow you to opt-out of our certain cookies, as they are necessary to ensure the proper functioning of our website (such as prompting our cookie banner and remembering your privacy choices) and/or to monitor site performance. These cookies are not used in a way that constitutes a “sale” of your data under the CCPA. You can set your browser to block or alert you about these cookies, but some parts of the site will not work as intended if you do so. You can usually find these settings in the Options or Preferences menu of your browser. Visit www.allaboutcookies.org to learn more.
Sale of Personal Data
We also use cookies to personalize your experience on our websites, including by determining the most relevant content and advertisements to show you, and to monitor site traffic and performance, so that we may improve our websites and your experience. You may opt out of our use of such cookies (and the associated “sale” of your Personal Information) by using this toggle switch. You will still see some advertising, regardless of your selection. Because we do not track you across different devices, browsers and GEMG properties, your selection will take effect only on this browser, this device and this website.
Social Media Cookies
We also use cookies to personalize your experience on our websites, including by determining the most relevant content and advertisements to show you, and to monitor site traffic and performance, so that we may improve our websites and your experience. You may opt out of our use of such cookies (and the associated “sale” of your Personal Information) by using this toggle switch. You will still see some advertising, regardless of your selection. Because we do not track you across different devices, browsers and GEMG properties, your selection will take effect only on this browser, this device and this website.
Targeting Cookies
We also use cookies to personalize your experience on our websites, including by determining the most relevant content and advertisements to show you, and to monitor site traffic and performance, so that we may improve our websites and your experience. You may opt out of our use of such cookies (and the associated “sale” of your Personal Information) by using this toggle switch. You will still see some advertising, regardless of your selection. Because we do not track you across different devices, browsers and GEMG properties, your selection will take effect only on this browser, this device and this website.
Help us tailor content specifically for you: