Security from the start: Using DevOps for secure collaboration
By including security in all aspects of development and operations processes, agencies can move from a reactive to a proactive security posture.
Is predictive analytics really a game changer?
It may be too soon to tell, but predictive analytics offers agencies hope that they can get ahead of the threat rather than just cleaning up after the fact.
One year after OPM breach, cyber execs see little improvement
A new report shows nearly 60 percent of respondents believe that their agency currently struggles to understand how cyberattackers can breach their systems.
Using active breach detection to keep government data safe
Next-generation breach detection marries big-data and machine learning to deep cybersecurity expertise to maximize defense against breaches and threats.
Vulnerabilities persist in TSA’s Security Technology Integrated Program
An inspector general audit reveals vulnerabilities in servers, outdated operating systems and physical and security deficiencies in the Transportation Security Administration system that connects airport security systems to central TSA servers.
Watson takes on cybersecurity
Watson for Cyber Security will leverage the platform’s natural language processing to provide insight to threats.
Next-gen networks call for strategic security
A hybrid approach to network modernization can be cost-effective for agencies and deliver real improvements in capacity, availability and security.
4 steps to secure data management
Establishing the right technology ecosystem can address agencies’ data security challenges, including how and where to store data and control access.
DISA evaluates DODIN defense through adversary’s eyes
The cybersecurity review examines the DODIN from an adversary’s perspective to better prepare network defenders.
NIST previews new federal authentication guidelines
The National Institute of Standards and Technology is calling on the public to help it map out new guidelines for federal agencies' digital authentication practices.
How ID can move out of the wallet and onto the smartphone
HID Global’s goID platform lets government agencies issue identity credentials over the air to users’ smartphones, from which they can transfer relevant ID data to requestors.
Lessons from tax season: 4 tips for preventing cyberattacks on the workforce
Scams targeting employees during this recent tax season serve as a sobering reminder of the significant security risks workers unknowingly pose to their organizations.
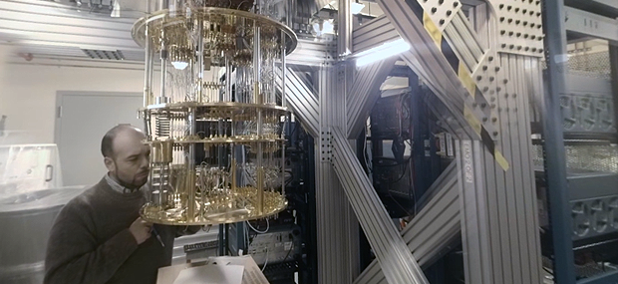
Prep for next-gen encryption should start yesterday
Because the effort to pull together any kind of quantum-resistant cryptography will be lengthy and complex, the process must start now if those trusted cryptosystems are to be developed in time.
Protecting data wherever it lives
Most of today’s encryption efforts focus on data stored on servers because that is where the majority of big breaches take place.
The encryption challenge
The obstacles are daunting -- money, time, careless users, encryption-resistant legacy systems. But the risks are no less serious.
Persistent tracking of endpoint devices takes on insider threats
Absolute’s Endpoint Data Discovery allows organizations to identify and protect sensitive data stored on endpoint devices outside the enterprise network.
Proving ground aims to spur rapid fielding of cyber tech
To counter the pace of cyberattacks, the new Air Force Cyber Proving Ground aims to rapidly get cyber tools to operators.
What comes after common access cards?
The future of authentication could start with mobile devices and apps that track user location and behavior, DISA Director Lt. Gen. Alan Lynn said.
Building on the cybersecurity sprint with CDM Phase II
Agencies that focus on a governance-based identity and access management strategy can protect against the full range of identity-centered attacks.
DOD officials push back on civil cyber support critiques
During a recent panel discussion, Pentagon officials pushed back on criticisms that there is lack of clarity on how the Defense Department will respond to domestic cyberattacks.

Do Not Sell My Personal Information
When you visit our website, we store cookies on your browser to collect information. The information collected might relate to you, your preferences or your device, and is mostly used to make the site work as you expect it to and to provide a more personalized web experience. However, you can choose not to allow certain types of cookies, which may impact your experience of the site and the services we are able to offer. Click on the different category headings to find out more and change our default settings according to your preference. You cannot opt-out of our First Party Strictly Necessary Cookies as they are deployed in order to ensure the proper functioning of our website (such as prompting the cookie banner and remembering your settings, to log into your account, to redirect you when you log out, etc.). For more information about the First and Third Party Cookies used please follow this link.
Manage Consent Preferences
Strictly Necessary Cookies - Always Active
We do not allow you to opt-out of our certain cookies, as they are necessary to ensure the proper functioning of our website (such as prompting our cookie banner and remembering your privacy choices) and/or to monitor site performance. These cookies are not used in a way that constitutes a “sale” of your data under the CCPA. You can set your browser to block or alert you about these cookies, but some parts of the site will not work as intended if you do so. You can usually find these settings in the Options or Preferences menu of your browser. Visit www.allaboutcookies.org to learn more.
Sale of Personal Data, Targeting & Social Media Cookies
Under the California Consumer Privacy Act, you have the right to opt-out of the sale of your personal information to third parties. These cookies collect information for analytics and to personalize your experience with targeted ads. You may exercise your right to opt out of the sale of personal information by using this toggle switch. If you opt out we will not be able to offer you personalised ads and will not hand over your personal information to any third parties. Additionally, you may contact our legal department for further clarification about your rights as a California consumer by using this Exercise My Rights link
If you have enabled privacy controls on your browser (such as a plugin), we have to take that as a valid request to opt-out. Therefore we would not be able to track your activity through the web. This may affect our ability to personalize ads according to your preferences.
Targeting cookies may be set through our site by our advertising partners. They may be used by those companies to build a profile of your interests and show you relevant adverts on other sites. They do not store directly personal information, but are based on uniquely identifying your browser and internet device. If you do not allow these cookies, you will experience less targeted advertising.
Social media cookies are set by a range of social media services that we have added to the site to enable you to share our content with your friends and networks. They are capable of tracking your browser across other sites and building up a profile of your interests. This may impact the content and messages you see on other websites you visit. If you do not allow these cookies you may not be able to use or see these sharing tools.
If you want to opt out of all of our lead reports and lists, please submit a privacy request at our Do Not Sell page.
Cookie List
A cookie is a small piece of data (text file) that a website – when visited by a user – asks your browser to store on your device in order to remember information about you, such as your language preference or login information. Those cookies are set by us and called first-party cookies. We also use third-party cookies – which are cookies from a domain different than the domain of the website you are visiting – for our advertising and marketing efforts. More specifically, we use cookies and other tracking technologies for the following purposes:
Strictly Necessary Cookies
We do not allow you to opt-out of our certain cookies, as they are necessary to ensure the proper functioning of our website (such as prompting our cookie banner and remembering your privacy choices) and/or to monitor site performance. These cookies are not used in a way that constitutes a “sale” of your data under the CCPA. You can set your browser to block or alert you about these cookies, but some parts of the site will not work as intended if you do so. You can usually find these settings in the Options or Preferences menu of your browser. Visit www.allaboutcookies.org to learn more.
Functional Cookies
We do not allow you to opt-out of our certain cookies, as they are necessary to ensure the proper functioning of our website (such as prompting our cookie banner and remembering your privacy choices) and/or to monitor site performance. These cookies are not used in a way that constitutes a “sale” of your data under the CCPA. You can set your browser to block or alert you about these cookies, but some parts of the site will not work as intended if you do so. You can usually find these settings in the Options or Preferences menu of your browser. Visit www.allaboutcookies.org to learn more.
Performance Cookies
We do not allow you to opt-out of our certain cookies, as they are necessary to ensure the proper functioning of our website (such as prompting our cookie banner and remembering your privacy choices) and/or to monitor site performance. These cookies are not used in a way that constitutes a “sale” of your data under the CCPA. You can set your browser to block or alert you about these cookies, but some parts of the site will not work as intended if you do so. You can usually find these settings in the Options or Preferences menu of your browser. Visit www.allaboutcookies.org to learn more.
Sale of Personal Data
We also use cookies to personalize your experience on our websites, including by determining the most relevant content and advertisements to show you, and to monitor site traffic and performance, so that we may improve our websites and your experience. You may opt out of our use of such cookies (and the associated “sale” of your Personal Information) by using this toggle switch. You will still see some advertising, regardless of your selection. Because we do not track you across different devices, browsers and GEMG properties, your selection will take effect only on this browser, this device and this website.
Social Media Cookies
We also use cookies to personalize your experience on our websites, including by determining the most relevant content and advertisements to show you, and to monitor site traffic and performance, so that we may improve our websites and your experience. You may opt out of our use of such cookies (and the associated “sale” of your Personal Information) by using this toggle switch. You will still see some advertising, regardless of your selection. Because we do not track you across different devices, browsers and GEMG properties, your selection will take effect only on this browser, this device and this website.
Targeting Cookies
We also use cookies to personalize your experience on our websites, including by determining the most relevant content and advertisements to show you, and to monitor site traffic and performance, so that we may improve our websites and your experience. You may opt out of our use of such cookies (and the associated “sale” of your Personal Information) by using this toggle switch. You will still see some advertising, regardless of your selection. Because we do not track you across different devices, browsers and GEMG properties, your selection will take effect only on this browser, this device and this website.
Help us tailor content specifically for you: