Using the NSA Intrusion Lifecycle to bolster security
Although enterprise security will never be perfect, the NSA lifecycle can give defenders a model for mapping the appropriate mitigation to each step in the intrusion process.
In 2015, agency IT security and operations converge
The new year will see a convergence of IT security and operations, as agencies spread responsibilities across IT departments and security tools become integrated into software lifecycles earlier .
Police body cameras are only one piece of the video equation
A federal initiative to help departments purchase 50,000 body cameras for police in the wake of recent high-profile incidents of police violence is only the first step in creating a full video system. Departments will have to store and manage terabytes of data for years, sometimes decades.
Will CDM finally be ‘the realization of IT security’?
Tools and services are being chosen for Phase 2 of the Continuous Diagnostics and Mitigation program, which security watchers say could be a revolutionary step in how the government protects its information.
Cybersecurity’s not done until the paperwork is finished
The VA has been dinged – again – by the GAO because of incomplete follow-through in its cybersecurity operations, showing that it takes more than mere box-checking to make regulators happy.
NIST marks top security requirements for government cloud
NIST’s cloud computing roadmap recommends actions to ensure that cloud computing offerings meet the security needs of government as well as the requirements of multiple tenants.
CIOpedia remains go-to source for CIO trade secrets
The CIOpedia, a part of the CIO Council’s Knowledge Portal, provides a source of best practices in managing the government’s complex information environment.
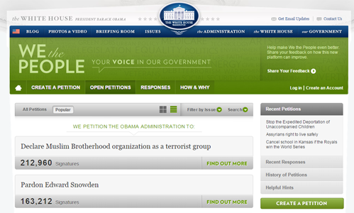
API expands 'We the People' petitions
The new Write API for the We the People petition site aims to let users sign online petitions from a variety of platforms and sites without visiting the White House page.
Critics await 'The Return of Open Enrollment'
When online health insurance exchanges failed to perform as expected during the Affordable Care Act’s first open enrollment period, call centers became a vital backup. How will things roll in the upcoming OE2?
How a city’s SCADA upgrade turned bandwidth into revenue
The city of Piqua, Ohio, took advantage of the need to replace an aging SCADA network by building enough bandwidth to serve city needs, with some left over to sell.
Taking aim at stealthy attacks
The recent SandWorm report on cyber espionage against NATO highlights the need for strategies such as the cyber kill chain to detect and disable stealthy, zero-day threats before they bleed you dry.
Cole guides agencies in next-gen cyber warfare
As FireEye's global government liaison, Tony Cole brings governments the technology and insights to thwart a new generation of motivated attackers.
AppVet speeds mobile devices, apps to the battlefield
The NIST AppVet project developed a framework to evaluate hardware and software for off-the-shelf smartphones in military field operations.
Hoping higher FISMA scores mean more than compliance
Growing resources and increasing attention being paid to continuous monitoring could help agencies consolidate last year's gains in FISMA performance.
FEMA opened flood risk tools to property owners
The Federal Emergency Management Agency opened up high-quality flood risk data to property owners, improving public awareness and promoting risk mitigation.
Access controls fall short in most agencies
According to the GAO, inadequate access control is a common weakness across 24 major agencies.
Passwords vs. biometrics
It’s not a competition, but neither provides completely secure or effective access control on its own. What is needed is an appropriate combination of technologies.
How to re-engineer for automation
In automating a workflow process, the success depends largely on how well the underlying process has been designed.
Document workflow keeps up with county's growing needs, shrinking budget
Replacing paper with digital documents and case management tools helped Durham County, N.C., fill the gaps between workflow demands and workforce resources.
Do you know where your mobile data is?
Recent hacks of celebrity data that had been saved to the cloud illustrate the need to be aware of what your mobile devices – agency-issued or BYOD – are doing and where the data is going.

Do Not Sell My Personal Information
When you visit our website, we store cookies on your browser to collect information. The information collected might relate to you, your preferences or your device, and is mostly used to make the site work as you expect it to and to provide a more personalized web experience. However, you can choose not to allow certain types of cookies, which may impact your experience of the site and the services we are able to offer. Click on the different category headings to find out more and change our default settings according to your preference. You cannot opt-out of our First Party Strictly Necessary Cookies as they are deployed in order to ensure the proper functioning of our website (such as prompting the cookie banner and remembering your settings, to log into your account, to redirect you when you log out, etc.). For more information about the First and Third Party Cookies used please follow this link.
Manage Consent Preferences
Strictly Necessary Cookies - Always Active
We do not allow you to opt-out of our certain cookies, as they are necessary to ensure the proper functioning of our website (such as prompting our cookie banner and remembering your privacy choices) and/or to monitor site performance. These cookies are not used in a way that constitutes a “sale” of your data under the CCPA. You can set your browser to block or alert you about these cookies, but some parts of the site will not work as intended if you do so. You can usually find these settings in the Options or Preferences menu of your browser. Visit www.allaboutcookies.org to learn more.
Sale of Personal Data, Targeting & Social Media Cookies
Under the California Consumer Privacy Act, you have the right to opt-out of the sale of your personal information to third parties. These cookies collect information for analytics and to personalize your experience with targeted ads. You may exercise your right to opt out of the sale of personal information by using this toggle switch. If you opt out we will not be able to offer you personalised ads and will not hand over your personal information to any third parties. Additionally, you may contact our legal department for further clarification about your rights as a California consumer by using this Exercise My Rights link
If you have enabled privacy controls on your browser (such as a plugin), we have to take that as a valid request to opt-out. Therefore we would not be able to track your activity through the web. This may affect our ability to personalize ads according to your preferences.
Targeting cookies may be set through our site by our advertising partners. They may be used by those companies to build a profile of your interests and show you relevant adverts on other sites. They do not store directly personal information, but are based on uniquely identifying your browser and internet device. If you do not allow these cookies, you will experience less targeted advertising.
Social media cookies are set by a range of social media services that we have added to the site to enable you to share our content with your friends and networks. They are capable of tracking your browser across other sites and building up a profile of your interests. This may impact the content and messages you see on other websites you visit. If you do not allow these cookies you may not be able to use or see these sharing tools.
If you want to opt out of all of our lead reports and lists, please submit a privacy request at our Do Not Sell page.
Cookie List
A cookie is a small piece of data (text file) that a website – when visited by a user – asks your browser to store on your device in order to remember information about you, such as your language preference or login information. Those cookies are set by us and called first-party cookies. We also use third-party cookies – which are cookies from a domain different than the domain of the website you are visiting – for our advertising and marketing efforts. More specifically, we use cookies and other tracking technologies for the following purposes:
Strictly Necessary Cookies
We do not allow you to opt-out of our certain cookies, as they are necessary to ensure the proper functioning of our website (such as prompting our cookie banner and remembering your privacy choices) and/or to monitor site performance. These cookies are not used in a way that constitutes a “sale” of your data under the CCPA. You can set your browser to block or alert you about these cookies, but some parts of the site will not work as intended if you do so. You can usually find these settings in the Options or Preferences menu of your browser. Visit www.allaboutcookies.org to learn more.
Functional Cookies
We do not allow you to opt-out of our certain cookies, as they are necessary to ensure the proper functioning of our website (such as prompting our cookie banner and remembering your privacy choices) and/or to monitor site performance. These cookies are not used in a way that constitutes a “sale” of your data under the CCPA. You can set your browser to block or alert you about these cookies, but some parts of the site will not work as intended if you do so. You can usually find these settings in the Options or Preferences menu of your browser. Visit www.allaboutcookies.org to learn more.
Performance Cookies
We do not allow you to opt-out of our certain cookies, as they are necessary to ensure the proper functioning of our website (such as prompting our cookie banner and remembering your privacy choices) and/or to monitor site performance. These cookies are not used in a way that constitutes a “sale” of your data under the CCPA. You can set your browser to block or alert you about these cookies, but some parts of the site will not work as intended if you do so. You can usually find these settings in the Options or Preferences menu of your browser. Visit www.allaboutcookies.org to learn more.
Sale of Personal Data
We also use cookies to personalize your experience on our websites, including by determining the most relevant content and advertisements to show you, and to monitor site traffic and performance, so that we may improve our websites and your experience. You may opt out of our use of such cookies (and the associated “sale” of your Personal Information) by using this toggle switch. You will still see some advertising, regardless of your selection. Because we do not track you across different devices, browsers and GEMG properties, your selection will take effect only on this browser, this device and this website.
Social Media Cookies
We also use cookies to personalize your experience on our websites, including by determining the most relevant content and advertisements to show you, and to monitor site traffic and performance, so that we may improve our websites and your experience. You may opt out of our use of such cookies (and the associated “sale” of your Personal Information) by using this toggle switch. You will still see some advertising, regardless of your selection. Because we do not track you across different devices, browsers and GEMG properties, your selection will take effect only on this browser, this device and this website.
Targeting Cookies
We also use cookies to personalize your experience on our websites, including by determining the most relevant content and advertisements to show you, and to monitor site traffic and performance, so that we may improve our websites and your experience. You may opt out of our use of such cookies (and the associated “sale” of your Personal Information) by using this toggle switch. You will still see some advertising, regardless of your selection. Because we do not track you across different devices, browsers and GEMG properties, your selection will take effect only on this browser, this device and this website.